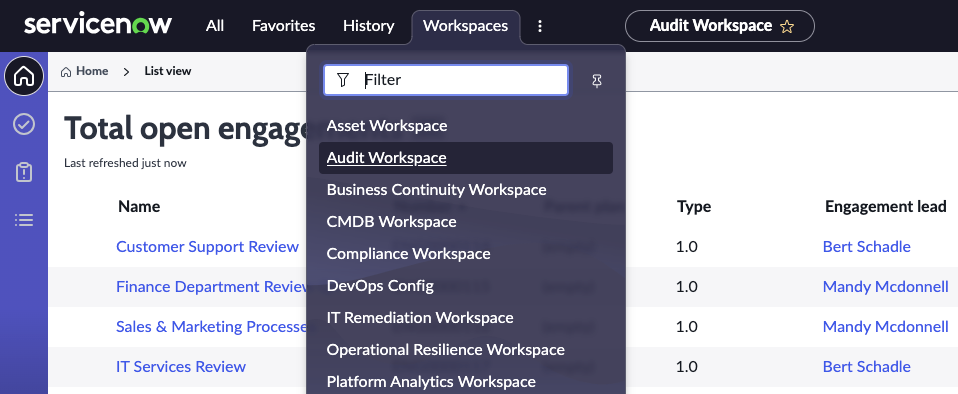
If you’re interested in ServiceNow GRC (Governance Risk and Compliance), start with learning the Auditor Workspace and Audit Management.
Auditor Workspace: https://docs.servicenow.com/bundle/vancouver-governance-risk-compliance/page/product/grc-workspace-audit/concept/audit-management-overview-ws.html
Audit Management https://docs.servicenow.com/bundle/vancouver-governance-risk-compliance/page/product/grc-audit/concept/c_GRCAudits.html
Governance: The frameworks of an organization’s activities and whether or not they are aligned with business objectives. Activities include processes, structures, and policies that are meant to manage and monitor company activities.
Risk: A sustained process of addressing risks, mitigating risks through controls, and providing assurance that the risks are managed according to policies. This includes measurement of risk, assessment, retention, monitoring, and identification.
Compliance: Ensuring that activities within an organization operate in a way that are aligned with laws and regulations.
*From https://www.servicenow.com/products/governance-risk-and-compliance/what-is-grc.html
ServiceNow documentation for Governance,Risk, and Compliance:
https://docs.servicenow.com/csh?topicname=r_WhatIsGRC.html&version=latest

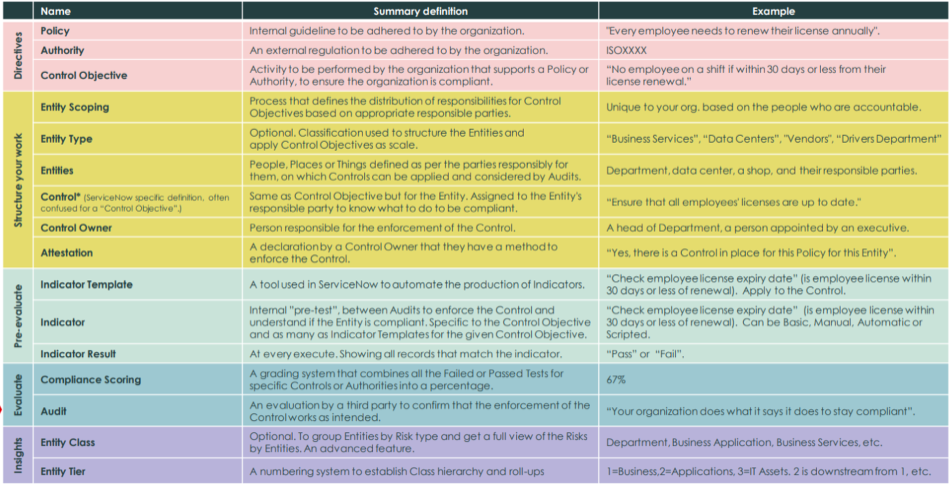
The following glossary comes from Navex Global. We enhanced it with links to supporting documentation, some of which is specific to ServiceNow how-tos and links to their documentation. https://www.navexglobal.com/compliancenext/understanding-the-basics/pocket-guide-to-compliance-terminology-2/
Audit
An examination performed that verifies the guidelines outlined by a regulatory body.
https://docs.servicenow.com/csh?topicname=audit-management-overview-ws.html&version=latest
Attestation
The acknowledgement of understanding and abidance to policies, procedures or training.
Within ServiceNow, navigate to: Policy and Compliance > Controls > My Attestations
https://docs.servicenow.com/csh?topicname=attest-a-control.html&version=latest

Authority
Authority Documents
Authority documents refer to written documents that establish and communicate the organizational policies, procedures, guidelines, and standards governing various aspects of operations. These documents serve as a foundation for governance, outlining the rules and expectations that guide decision-making, actions, and behavior within an organization.
To create an authority document, navigate to All > Policy and Compliance > Authority Documents

Here’s the ServiceNow documentation:
https://docs.servicenow.com/csh?topicname=t_CreateAnAuthorityDocument.html&version=latest
For a deeper dive into authority documents, click here.
Benchmarking
Analyzing your data year over year by comparing one’s own business processes and performance against the industry standard to reveal compliance program effectiveness and determine needed improvements.
Here is the documentation for how benchmarks work within ServiceNow:
Blockchain
A blockchain is a digitized, decentralized, public ledger of all cryptocurrency transactions. Growing as completed blocks, the most recent transactions are recorded and added to the chain in chronological order allowing market participants to track digital currency transactions without central recordkeeping. Each node (a computer connected to the network) gets a copy of the blockchain that is downloaded automatically.
Originally developed as the accounting method for the virtual currency Bitcoin, blockchains use what is now known as distributed ledger technology (DLT). This technology creates indelible records that cannot be changed, as the authenticity can be verified by the entire community using the blockchain instead of a single centralized authority.
See this excerpt from Nicola Attico’s article on LinkedIN, and follow him if you’re interested in creating low code apps on ServiceNow, or bringing data from the blockchain into ServiceNow: https://www.linkedin.com/pulse/low-code-blockchain-applications-servicenow-provide-nicola-attico/
“In this prototype, which has been built for the Enterprise Ethereum Alliance Conference “Ethereum in the Enterprise 2021”, ServiceNow connects to the Ethereum public network (Ropsten, in fact) through a ServiceNow scoped application, that works as a connector to the Provide Stack, making available a full API and Integration Hub spoke. That allows other applications on the same ServiceNow instance –either native application or custom applications– to seamlessly connect to Ethereum and other blockchains. This connector application is able to make full use of Provide Services, including Ident, Vault, Nchain, Payments, Privacy, and Shuttle (aka baselining).”
Bribe
An incentive given or offered to a person or organization to encourage that person/organization to take an action that benefits the giver of the bribe. ISO 37001 covers anti corruption and bribery. https://www.iso.org/iso-37001-anti-bribery-management.html
Chief Privacy Officer
A chief privacy officer (CPO) is a corporate executive charged with developing and implementing policies designed to protect employee and customer data from unauthorized access.
If you’re looking for a new Chief Privacy Officer, try this Google X-ray search. Just go to Google and type this in the search bar. Try it in Bing or other search engines as well:
inurl:linkedin.com/in “chief privacy officer” los angeles
See our x-ray search page for more.
Chief Risk Officer
The chief risk officer (CRO) is the corporate executive tasked with assessing and mitigating significant competitive, regulatory and technological threats to an enterprise’s capital and earnings. The position is sometimes called chief risk management officer or simply risk management officer.
If you are searching for Chief Risk Officers to connect with on LinkedIN, try this Google X-ray search:
inurl:linkedin.com/in “chief risk officer” los angeles
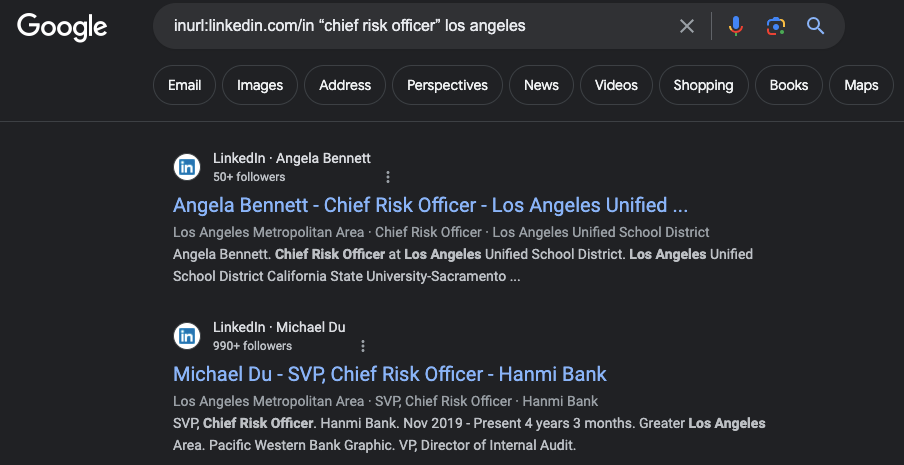
For more tips on finding people, check out the X-ray search page here.
Code of Conduct or Code of Ethics
An organization’s Code of Conduct is its policy of all policies. It’s a central guide and reference for users in support of day-to-day decision making. It is meant to clarify an organization’s mission, values and principles, linking them with standards of professional conduct. As a reference, it can be used to locate relevant documents, services and other resources related to ethics within the organization.
Indeed has a good article and template for writing / editing a code of conduct: https://www.indeed.com/hire/c/info/write-a-code-of-conduct
Compliance
Compliance is either a state of being in accordance with established guidelines or specifications, or the process of becoming so. Common frameworks are:
ISO 27001
ISO/IEC 27001 is an international standard for information security management systems (ISMS). Published by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC), ISO 27001 provides a systematic and structured approach to managing and securing sensitive information within an organization.
NIST 800-53
CIS Controls The Cybersecurity Controls Accelerator contains the CIS Controls version 7.1 authority document, 191 associated CIS citations, and 191 CIS control objectives that are related to the citations.
https://docs.servicenow.com/csh?topicname=cybersecurity-controls-accelerator.html&version=latest
HIPAA – The Health Insurance Portability and Accountability Act of 1996 (HIPAA) required the Secretary of the U.S. Department of Health and Human Services (HHS) to develop regulations protecting the privacy and security of certain health information.1 To fulfill this requirement, HHS published what are commonly known as the HIPAA Privacy Rule and the HIPAA Security Rule. The Privacy Rule, or Standards for Privacy of Individually Identifiable Health Information, establishes national standards for the protection of certain health information.
SOX The Sarbanes-Oxley (SOX) Content Pack provides basic SOX content for an organization to commence and manage activities towards attaining operational SOX compliance using the ServiceNow® GRC application. A content pack may include pre-defined scope, specific policies, controls, risks, audit, test plans, dashboards, and reports providing users of ServiceNow® GRC a head-start in using the applications towards SOX compliance-related activities. https://docs.servicenow.com/bundle/vancouver-governance-risk-compliance/page/product/grc-sox-compliance-content-pack/concept/sn-store-SOX-governance-risk-compliance.html
GLBA
The Gramm-Leach-Bliley Act (GLBA), also known as the Financial Services Modernization Act of 1999, is a United States federal law that aims to enhance consumer privacy and security in the financial industry. The GLBA consists of three main sections, each addressing different aspects of consumer financial privacy.
GLBA is crucial for financial institutions to maintain the trust of their customers and avoid legal and regulatory consequences. Financial institutions subject to GLBA must implement and maintain comprehensive privacy and security programs, conduct risk assessments, provide clear and timely notices to customers, and establish measures to prevent unauthorized access to customer information. Non-compliance with GLBA can lead to regulatory penalties and reputational damage. Organizations should regularly assess and update their privacy and security practices to ensure ongoing compliance with GLBA requirements.
The key concepts of compliance for GLBA include:
Privacy Rule:The Privacy Rule of the GLBA establishes requirements for the privacy and security of consumers’ nonpublic personal information (NPI) held by financial institutions.
Key Concepts: Financial institutions must provide clear and conspicuous notices to customers about their privacy policies and practices.
Opt-Out: Customers have the right to opt out of having their nonpublic personal information shared with non-affiliated third parties.
Security Measures: Financial institutions are required to implement security measures to protect the confidentiality and integrity of customers’ NPI.
Safeguards Rule: The Safeguards Rule outlines the requirements for financial institutions to establish and maintain an information security program to protect customers’ nonpublic personal information.
Risk Assessment: Financial institutions must conduct a thorough risk assessment to identify and assess potential risks to the security, confidentiality, and integrity of customer information.
Security Program: Develop, implement, and maintain a comprehensive information security program that includes administrative, technical, and physical safeguards.
Employee Training: Provide regular training to employees regarding the importance of safeguarding customer information and the specific measures in place.
Pretexting Provisions: The GLBA includes provisions aimed at preventing pretexting, which involves obtaining personal financial information under false pretenses.
Prohibition of Pretexting: The act explicitly prohibits the practice of obtaining customer information through false pretenses or fraudulent activities.
Customer Authentication: Financial institutions must implement measures to authenticate the identity of customers before disclosing nonpublic personal information.
Financial Privacy Rule: The Financial Privacy Rule of the GLBA governs the collection and disclosure of customers’ personal financial information by financial institutions.
Limits on Disclosure: Financial institutions are restricted in the disclosure of nonpublic personal information to non-affiliated third parties.
Opt-Out Rights: Customers have the right to opt out of having their nonpublic personal information shared with non-affiliated third parties.
FISMA
GDPR
Compliance Audit
A compliance audit is a comprehensive review of an organization’s adherence to regulatory guidelines. Independent accounting, security or IT consultants evaluate the strength and thoroughness of compliance preparedness. Auditors review security polices, user access controls and risk management procedures over the course of a compliance audit
Compliance Burden
Compliance burden, also called regulatory burden, is the administrative cost of a regulation in terms of dollars, time and complexity
Compliance Framework
A compliance framework is a structured set of guidelines that details an organization’s processes for maintaining accordance with established regulations, specifications or legislation
Several compliance frameworks are widely utilized by organizations to ensure that they meet regulatory requirements, industry standards, and best practices. The choice of a specific framework often depends on factors such as the industry, geographic location, and the nature of the organization’s activities. Here are some of the most commonly utilized compliance frameworks:
ISO 27001 (Information Security Management System):
ISO 27001 is an international standard for information security management systems (ISMS). It provides a systematic approach to managing sensitive company information, ensuring its confidentiality, integrity, and availability. ISO 27001 is widely adopted by organizations globally.
https://www.iso.org/standard/27001
HIPAA (Health Insurance Portability and Accountability Act):
HIPAA is a U.S. regulatory framework that focuses on protecting the privacy and security of health information. It applies to healthcare providers, health plans, and healthcare clearinghouses, as well as their business associates.
https://www.hhs.gov/hipaa/index.html
PCI DSS (Payment Card Industry Data Security Standard):
PCI DSS is a set of security standards designed to ensure that all companies that accept, process, store, or transmit credit card information maintain a secure environment. It is particularly relevant to businesses in the payment card industry.
https://www.pcisecuritystandards.org/document_library
GDPR (General Data Protection Regulation):
GDPR is a European Union regulation that governs the protection of personal data of individuals. It applies to organizations that process or control personal data of EU citizens. GDPR has global implications, as organizations worldwide must comply when handling EU citizens’ data.
GDPR.EU has a useful guide here: https://gdpr.eu/
NIST Cybersecurity Framework:
Developed by the National Institute of Standards and Technology (NIST) in the United States, this framework provides a set of cybersecurity best practices that organizations can voluntarily adopt. It focuses on identifying, protecting, detecting, responding to, and recovering from cybersecurity threats.
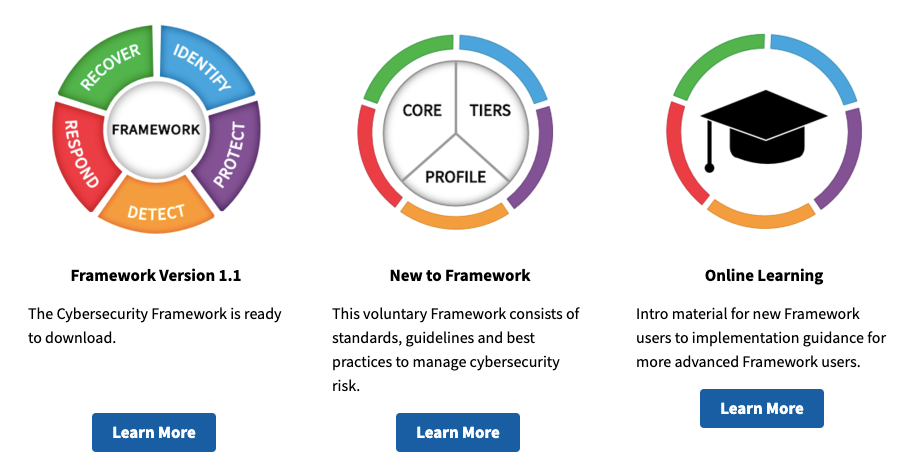
There is a NIST CSF use case accelerator you can check out at docs.servicenow.com:
https://docs.servicenow.com/csh?topicname=grc-csf-usecase-accelerator.html&version=latest
SOC 2 (Service Organization Control 2):
SOC 2 is a framework developed by the American Institute of CPAs (AICPA) for managing and securing sensitive data. A SOC 2 examination is a report on controls at a service organization relevant to security, availability, processing integrity, confidentiality, or privacy. SOC 2 reports are intended to meet the needs of a broad range of users that need detailed information and assurance about the controls at a service organization relevant to security, availability, and processing integrity of the systems the service organization uses to process users’ data and the confidentiality and privacy of the information processed by these systems.
https://www.aicpa-cima.com/resources/landing/system-and-organization-controls-soc-suite-of-services
COBIT (Control Objectives for Information and Related Technologies):
COBIT is a framework developed by ISACA for the governance and management of enterprise IT. It provides a comprehensive set of controls and best practices to help organizations achieve their business objectives.
https://www.isaca.org/resources/cobit
Control Objective
Control objectives serve as documentation of the organization’s intent and commitment to managing risks and complying with relevant regulations. This documentation is valuable for demonstrating due diligence in the event of audits or regulatory scrutiny.
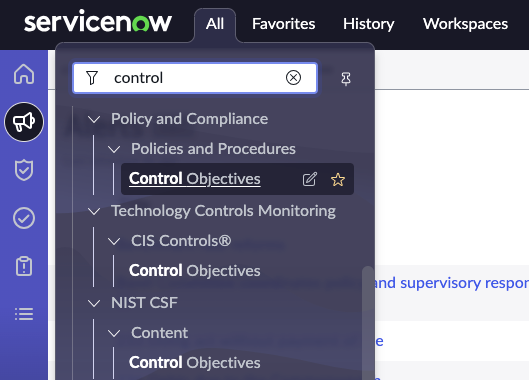
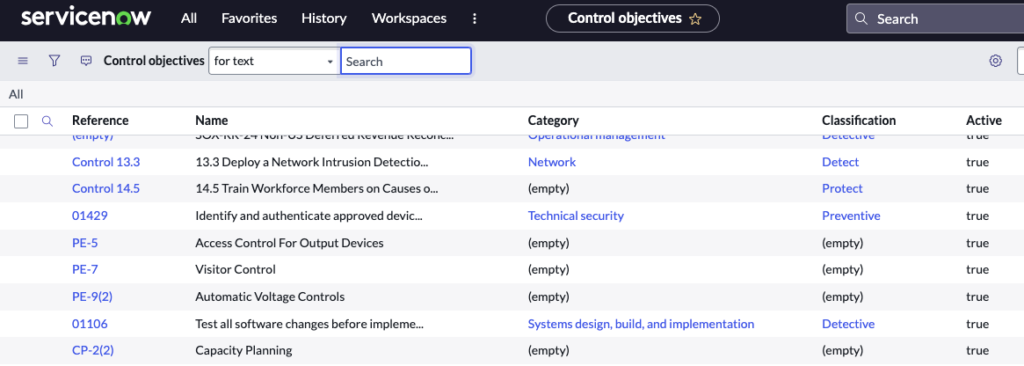
To create a new control objective, navigate to All > Policy and Compliance > Control Objectives. You’ll need one of the following roles: sn_compliance.admin, sn_compliance.manager, sn_compliance.user
Control Objectives in List View:
Entity
An entity is an organizational unit or element subject to governance and compliance oversight. Entities take various forms, and the term is often used to encompass different levels of organizational structure. For a list of what an entity can represent in GRC, click here.
ITIL (Information Technology Infrastructure Library):
ITIL is a set of practices for IT service management (ITSM) that focuses on aligning IT services with the needs of the business. It provides a framework for planning, delivering, and supporting IT services.
FFIEC (Federal Financial Institutions Examination Council):
FFIEC provides guidelines and standards for financial institutions in the United States. It covers areas such as information security, risk management, and cybersecurity.
FISMA (Federal Information Security Management Act):
FISMA is a U.S. federal law that defines a comprehensive framework to protect government information, operations, and assets against cybersecurity risks. It outlines requirements for federal agencies to develop, implement, and maintain information security programs.
Organizations often tailor these frameworks to their specific needs and circumstances. Additionally, some industries may have specific regulations and frameworks that organizations in those sectors must adhere to. It’s crucial for organizations to stay informed about changes in regulations and standards relevant to their industry and geographic location.
Compliance Risk
Compliance risk is exposure to legal penalties, financial forfeiture and material loss an organization faces when it fails to act in accordance with industry laws and regulations, internal policies or prescribed best practices
Controls
Corporate Governance
Corporate governance is a term that refers broadly to the rules, processes or laws by which businesses are operated, regulated and controlled. The term can refer to internal factors defined by the officers, stockholders or constitution of a corporation, as well as to external forces such as consumer groups, clients and government regulations
Cyber Security
Cyber security is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access.
Dodd-Frank Act
The Dodd-Frank Act (fully known as the Dodd-Frank Wall Street Reform and Consumer Protection Act) is a United States federal law that places regulation of the financial industry in the hands of the government. The legislation, enacted in July 2010, aims to prevent another significant financial crisis by creating new financial regulatory processes that enforce transparency and accountability while implementing rules for consumer protection.
https://www.sec.gov/securities-topics/dodd-frank-act
Ethical Dilemmas
Situations that require ethical judgment calls. Often, there is more than one right answer and no win-win solution in which we get everything we want.
Ethics
The decisions, choices and actions (behaviors) we make that reflect and enact our values
LinkedIN Learning has an Ethics course that has been viewed over 100,000 times. https://www.linkedin.com/learning/business-ethics
FCPA
The Foreign Corrupt Practices Act is a federal law enacted in 1977 to prohibit companies from paying bribes to foreign government officials and political figures for the purpose of obtaining business.
Released by the Department of Justice and the Securities and Exchange Commission, A Resource Guide to the U.S. Foreign Corrupt Practices Act, Second Edition, is a detailed compilation of information and analysis regarding the Foreign Corrupt Practices Act (FCPA).
Fraud
To intentionally lie or cheat to get something to which one is not entitled
General Data Protection Regulation (GDPR)
The General Data Protection Regulation (GDPR) is a legal framework that sets new guidelines for the collection and processing of personal information of individuals within the European Union (EU). The GDPR lays out the principles for data management and the rights of the individual, while also imposing fines that can be revenue-based. The General Data Protection Regulation applies to all organizations that deal with EU citizen data, making it a critical regulation for corporate compliance officers at banks, insurers, and other financial organizations. On May 25, 2018 GDPR will come into full-effect across the EU.
Governance
The act, process or power of exercising authority or control in an organizational setting.
Governance, Risk and Compliance (GRC)
Governance, Risk and Compliance (GRC) is a combined area of focus within an organization that developed because of interdependencies between the three components. GRC software products, available from a number of vendors, typically facilitate compliance with legal requirements, such as those specified in the Sarbanes-Oxley Act (SOX) or occupational health and safety regulations.
Gramm-Leach-Bliley Act (GLB)
Federal legislation enacted in the United States to control the ways that financial institutions deal with the private information of individuals
Hotline
A common reporting system giving anonymous telephone access to employees seeking to report possible instances of wrongdoing.
Integrity
Making choices that are consistent with each other and with the stated and operative values one espouses. Striving for ethical congruence in one’s decisions
Internal Control
An internal control is a business practice, policy or procedure that is established within an organization to create value or minimize risk
ITGC Information Technology General Controls
ITGC stands for Information Technology General Controls. These controls are a category of internal controls that are designed to ensure the reliability of information technology (IT) systems and data. ITGC controls play a fundamental role in managing and mitigating risks associated with IT operations. They are essential for maintaining the integrity, confidentiality, and availability of information within an organization’s IT environment.
Read more here.
NIST (National Institute of Standards and Technology)
A unit of the US Commerce Department that promotes and maintains measurement standards.
Ransomware
Ransomware is a type of malware (malicious software) distinct from other malware; its defining characteristic is that it attempts to deny access to a user’s data, usually by encrypting the data with a key known only to the hacker who deployed the malware, until a ransom is paid.
Regulatory Compliance
Regulatory compliance is an organization’s adherence to laws, regulations, guidelines and specifications relevant to its business. Violations of compliance regulations often result in legal punishment, including federal fines.
Risk Assessment
Risk assessment is the process of identifying variables that have the potential to negatively impact an organization’s ability to conduct business
Risk Assessment Framework (RAF)
A risk assessment framework (RAF) is a strategy for prioritizing and sharing information about the security risks to an information technology (IT) infrastructure
Risk Exposure
Risk exposure is a quantified loss potential of business. Risk exposure is usually calculated by multiplying the probability of an incident occurring by its potential losses
Sarbanes-Oxley Act (SOX)
The Sarbanes-Oxley Act of 2002 (often shortened to SOX) is legislation passed by the U.S. Congress to protect shareholders and the general public from accounting errors and fraudulent practices in the enterprise, as well as improve the accuracy of corporate disclosures. The U.S. Securities and Exchange Commission (SEC) administers the act, which sets deadlines for compliance and publishes rules on requirements
TPRM Third Party Risk Management
Transparency
Transparency, in a business or governance context, is honesty and openness. Transparency and accountability are generally considered the two main pillars of good corporate governance
Values
The core beliefs we hold regarding what is right and fair in terms of our actions and our interactions with others. Another way to characterize values is that they are what an individual believes to be of worth and importance to their life
Values-centered Code of Ethics
Offers a set of ethical ideals, such as integrity, trust-worthiness and responsibility, which companies want employees to adopt in their work practices
Whistleblower
A whistleblower is a person who voluntarily provides information to the general public, or someone in a position of authority, about dishonest or illegal business activities occurring at an organization. This organization could include a government department, a public company or a private organization
Workplace Harassment
As defined by the Equal Employment Opportunity Commission (EEOC):
Harassment is unwelcome conduct that is based on race, color, religion, sex (including pregnancy), national origin, age (40 or older), disability or genetic information. Harassment becomes unlawful where 1) enduring the offensive conduct becomes a condition of continued employment, or 2) the conduct is severe or pervasive enough to create a work environment that a reasonable person would consider intimidating, hostile, or abusive. Anti-discrimination laws also prohibit harassment against individuals in retaliation for filing a discrimination charge, testifying, or participating in any way in an investigation, proceeding, or lawsuit under these laws; or opposing employment practices that they reasonably believe discriminate against individuals, in violation of these laws.
Petty slights, annoyances, and isolated incidents (unless extremely serious) will not rise to the level of illegality. To be unlawful, the conduct must create a work environment that would be intimidating, hostile, or offensive to reasonable people.